In the cryptocurrency world, there’s a fundamental truth that every investor must understand: “Not your keys, not your crypto.”
- What is a Private Key? (Explained Simply)
- How Private Keys Work: Public-Key Cryptography Explained
- Private Key vs. Seed Phrase: What’s the Difference?
- Why “Not Your Keys, Not Your Crypto” is True
- The 5 Golden Rules of Private Key Security (2026 Edition)
- What To Do If Your Key is Compromised
- Conclusion: Freedom Requires Responsibility
This saying refers to private keys—the digital passwords that prove you own your cryptocurrency. Unlike traditional banking where institutions hold your funds, cryptocurrency puts you in complete control. But with great power comes great responsibility.
In 2026, over 80% of cryptocurrency thefts are linked to compromised private keys. Understanding what private keys are, how they work, and how to protect them isn’t just recommended—it’s essential for anyone serious about cryptocurrency ownership.
Must Read:
What is a Private Key? (Explained Simply)
Technically, a Private Key is a randomly generated string of alphanumeric characters (like a super-complex password) that allows funds to be spent from a specific crypto address. But technical definitions are boring. Let’s use a real-world analogy.
Think of your crypto wallet like a see-through mailbox on the street.
- Public Key (The Address): This is the mail slot. You can give this address to anyone. They can walk up and drop money (crypto) inside. They can see what’s inside, but they can’t take anything out.
- Private Key (The Key): This is the physical key that opens the mailbox. Only the person holding this key can unlock the box and take the money out to spend it.
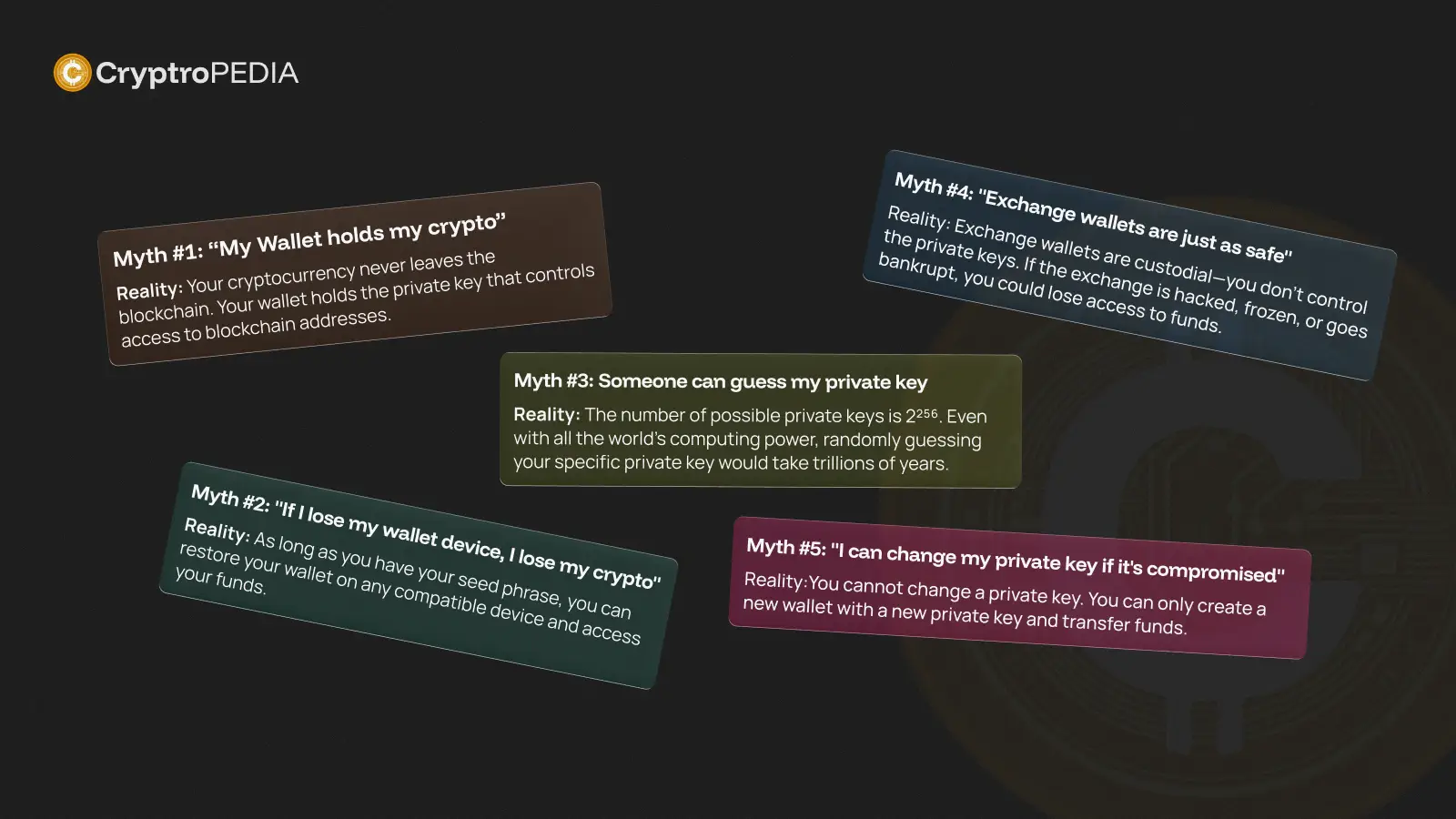
Reality Check
If you lose the key to your physical mailbox, a locksmith can drill it open. In crypto, there is no locksmith. If you lose your private key, that money stays in the mailbox forever, untouchable by anyone—including you.
How Private Keys Work: Public-Key Cryptography Explained
Private keys are based on public-key cryptography (also called asymmetric cryptography), a mathematical system that’s been securing digital communications since the 1970s.
Here’s how the system works:
Private Key Generation
- When you create a crypto wallet, it randomly generates a private key
- This number is so large (2256 possibilities for Bitcoin) that guessing it is mathematically impossible
- The chance of generating the same private key twice is effectively zero
Public Key Derivation
- Your private key is run through a one-way mathematical function
- This creates your public key
- ✅ Private key → Public key (easy)
- ❌ Public key → Private key (impossible)
Address Creation
- The public key goes through additional hashing
- This produces your cryptocurrency address
- This is what you share with others to receive payments
When you send cryptocurrency, your private key creates a digital signature that proves ownership.
Step-by-step transaction process:
- You initiate a transaction (send 0.1 BTC to Alice)
- Your wallet creates a transaction with details (amount, recipient address)
- Your private key “signs” the transaction using cryptographic algorithms
- The signature is broadcast to the blockchain network
- Network nodes verify the signature matches your public key
- Transaction is approved and added to the blockchain
- Funds are transferred – Alice now controls those coins
Example: Alice Sends Bitcoin to Bob
- Alice wants to send Kevin 0.5 BTC
- Alice’s wallet: “I’ll create a transaction moving 0.5 BTC from Alice’s address to Kevin’s address”
- Alice’s private key signs: Creates unique cryptographic signature
- Broadcast to network: “Here’s a signed transaction from Alice”
- Bitcoin network checks: “Does this signature match Alice’s public key?” → Yes ✓
- Transaction confirmed: Kevin receives 0.5 BTC
If someone tried to fake this transaction without Alice’s private key, the signature wouldn’t match her public key, and nodes would reject it.
Private Key vs. Seed Phrase: What’s the Difference?
This is where 90% of beginners get confused. You rarely see your raw Private Key. Instead, you see a Seed Phrase.
| Feature | Private Key | Seed Phrase (Recovery Phrase) |
|---|---|---|
| What it looks like | KwDiBf89QgGzgPs... (64 gibberish characters) | witch collapse practice feed... (12-24 words) |
| Readability | impossible to memorize | Human-readable and writable |
| Scope | Controls ONE specific address | Master Key that controls ALL addresses in your wallet |
| User Action | You rarely touch this directly | You MUST back this up safely |
| Recovery | Restores single address | Restores entire wallet |
| Standard | Raw cryptographic key | BIP39 standard (Bitcoin Improvement Proposal) |
| Typical use | Advanced/technical users | Everyday cryptocurrency users |
💡 Pro Tip: Think of the Seed Phrase as the “Master Key” ring. If you have a wallet with Bitcoin, Ethereum, and Solana, your Seed Phrase generates the specific Private Keys for all of them. Protect the Seed Phrase with your life.
Why “Not Your Keys, Not Your Crypto” is True
Ownership in crypto isn’t about your name being in a database. The blockchain doesn’t know who “John Smith” is. It only knows:
Whoever holds the private key for Address X has the right to move these funds.
Syed Safwan Abbas
The Custodial Trap (Exchange Wallets)
When you keep your coins on an exchange like Binance or Coinbase:
- They hold the private keys.
- You hold a login password.
If the exchange freezes your account, goes bankrupt (like FTX), or gets hacked, you have no recourse. You don’t actually own the crypto, you own an IOU.
True Ownership (Non-Custodial Wallets)
When you move crypto to your own wallet (like MetaMask or Ledger):
- You hold the private keys.
- No one can censor your transaction.
- No one can freeze your funds.
The 5 Golden Rules of Private Key Security (2026 Edition)
Security isn’t about being a tech genius; it’s about following strict habits. In 2026, where AI-driven scams are common, these rules are non-negotiable.
Rule 1: NEVER Share Your Seed Phrase
Legitimate support teams, wallet apps, or “validation services” will NEVER ask for your seed phrase.
- If a website asks for it? Scam.
- If “MetaMask Support” DMs you for it? Scam.
- Action: Treat your seed phrase like your bank PIN, but 100x more secret.
Rule 2: Don’t Screenshot It (The “No Digital” Rule)
Do not take a picture of your seed phrase. Do not save it in a text file. Do not email it to yourself.
- Why? Apps, malware, and cloud backups scan photos and text for 12-word patterns. If your phone gets hacked, your photo gallery is the first place they look.
- Action: Write it down on paper or steel.
Rule 3: Use Physical Backups
Paper is good; metal is better.
- Paper: Write it clearly. Store it in a fireproof/waterproof bag.
- Metal: For portfolios over $2,000, buy a steel backup (like Cryptosteel). It survives house fires and floods.
Rule 4: Double-Check Your Work
The most painful way to lose crypto is writing down a word wrong.
- The Test: When you set up a new wallet, write down the seed phrase, send $5 to it, delete the wallet, and try to recover it.
- Success? Now you can deposit your savings.
Rule 5: Beware of “Smart” Clipboards
Malware exists that detects when you copy a crypto address and replaces it with the hacker’s address.
- Action: Always verify the first 4 and last 4 characters of an address before clicking send.
What To Do If Your Key is Compromised
If you think someone saw your seed phrase, or you clicked a malicious link:
- Don’t Panic, But Move Fast. Minutes matter.
- Create a New Wallet immediately (on a different device if possible).
- Transfer ALL funds to the new wallet.
- Abandon the Old Wallet. Never use it again. It is “burned.”
You cannot “change” a private key like a password. You must evacuate the burning building and move to a new one.
Learn more: Crypto Wallets Explained
Conclusion: Freedom Requires Responsibility
Private keys are the ultimate tool of financial freedom. They give you power that no human in history had before 2009: the ability to transport millions of dollars anywhere in the world, instantly, without asking permission.
But that freedom comes with a price: You are responsible for your own security.
Treat your private key with the respect it deserves. Secure it offline, never share it, and you will sleep soundly knowing your digital wealth is truly yours.
Can I memorize my seed phrase (“Brain Wallet”)?
Don’t do it. Human memory is fallible. A car accident or simple forgetfulness could erase your wealth. Always have a physical backup.
Can two people have the same private key?
Mathematically, yes. Practically, no. The odds are like winning the lottery 10 times in a row while being struck by lightning. It’s statistically impossible.
What happens to my crypto if my hardware wallet breaks?
Nothing! Your crypto is on the blockchain, not the device. Buy a new device, enter your Seed Phrase, and your funds are there.